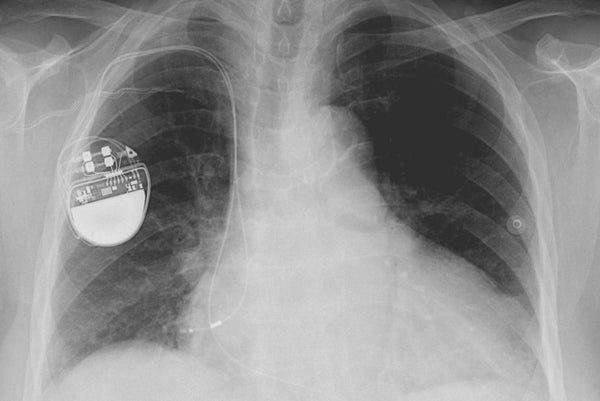
The U.S. government on Tuesday issued rules for addressing cyber vulnerabilities in medical devices, providing manufacturers with guidelines for fixing security bugs in equipment, including pacemakers, insulin pumps and imaging systems.
"Cybersecurity threats are real, ever-present and continuously changing," Suzanne Schwartz, a senior Food and Drug Administration official who helped draft the new rules, said in a blog post. "And as hackers become more sophisticated, these cybersecurity risks will evolve."
The FDA released the 30-page guidance as the agency investigates claims from a short-selling firm and security researchers that heart devices from St. Jude Medical Inc are vulnerable to life-threatening hacks. The allegations, which surfaced in August, underscore the need for clear government rules on identifying and mitigating the impact of security vulnerabilities in medical equipment.
On supporting science journalism
If you're enjoying this article, consider supporting our award-winning journalism by subscribing. By purchasing a subscription you are helping to ensure the future of impactful stories about the discoveries and ideas shaping our world today.
The FDA has been grappling with such issues for several years in response to a surge in research on potentially life- threatening security bugs in medical devices from so-called "white hat" hackers looking to identify flaws before they are exploited to harm patients.
The agency in 2014 issued guidance on how manufacturers should address cyber security when developing new products, though the rules did not cover equipment that was already on the market.
In 2015 the FDA advised hospitals to halt use of one of Hospira Inc's infusion pumps, saying a security vulnerability could allow cyber attackers to take remote control of the system.
The new guidelines detail how manufacturers should identify and fix cyber vulnerabilities in products that are already on the market. The rules encourage medical device makers to establish programs to make it easy for security researchers to report new bugs.
"There is greater clarity for manufacturers, patients and hospitals," said Josh Corman, an expert on medical device security who is director of the Atlantic Council's Cyber Statecraft Initiative.