
Content Mining: Not Just An Illustrator's Problem Anymore
Now everyone faces the same problem that illustrators have faced since the internet started.

Content Mining: Not Just An Illustrator's Problem Anymore
Now everyone faces the same problem that illustrators have faced since the internet started.

#BlackLivesMatter but Does Black Tech Expertise Matter, too?
My thoughts on timeing of Twitter's @BlackBirds & #AskDeRay activity in light of the critiques of Leslie Miley, for engineer for the organization, and the general Diversity environment in Tech and STEM in general.

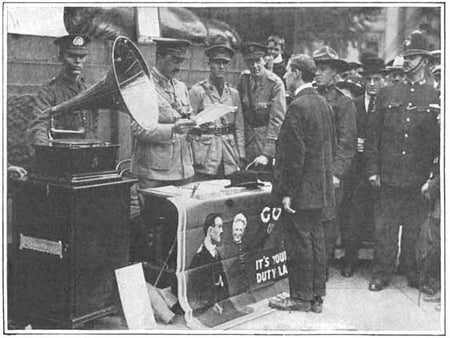
The Phonograph Goes to War, 1915

Sex: Seniors Find Answers Online
Older adults are seeking support and carnal knowledge from peers
Why Businesses Embrace Machine Learning [Excerpt]
The best algorithms determine who wins and loses in a digital economy that thrives on steering the consumer toward an opportune click

A Quick Guide to the Senate's Newly Passed Cybersecurity Bill
The basics of the controversial Cybersecurity Information Sharing Act (CISA)
Political and Industry Leaders Make a Case for Basic Research
At the “Innovation: An American Imperative” symposium October 20 on Capitol Hill, industry leaders and members of Congress talked about shoring up federal support for basic research and development

Jazz-Playing Robots Will Explore Human–Computer Relations
MUSICA is part of a new DARPA program to explore new ways that people can interact with computers and robots

Apple Thins iPhone Cloud Connections
The company’s moves to have iPhones be less dependent on the cloud and to be more encrypted could mean more user privacy

Back to the Future, Part II Predicted Techno-Marvels of October 21, 2015
Mr. Fusion aside, this 1989 time-traveling comedy was spot-on about many devices that we now take for granted

Verizon's Zombie Cookie Gets New Life
Verizon is merging its cellphone tracking supercookie with AOL’s ad tracking network to match users’ online habits with their offline details

Upcoming Streamed Talk: Future-Proofing Dinosaur Tattoos
How do you future-proof a dinosaur tattoo design?
This Thursday, October 8th Symbiartic's Glendon Mellow will be at Ryerson University's new launched Social Media Lab exploring how we communicate science through social media, specifically while using images. And it's going to be live streamed on Periscope!