
Massive CrowdStrike Tech Outage Highlights Global Vulnerabilities
Companies and governments alike need to step up cybersecurity practices in the wake of massive technology failures associated with a CrowdStrike update

Massive CrowdStrike Tech Outage Highlights Global Vulnerabilities
Companies and governments alike need to step up cybersecurity practices in the wake of massive technology failures associated with a CrowdStrike update

Artificial Intelligence Will Let Humanity Talk to Alien Civilizations
Large language models may enable real-time communication with extraterrestrial civilizations despite the vast distances between stars. We need to start thinking about what to tell them about us


Worldwide Tech Outage Started with Defective Crowdstrike Update to Microsoft Windows
An issue with a commonly used security software called Crowdstrike shuttered large technology systems around the globe, including airlines, transit systems and stock exchanges

AI's Bullshitting Obscures Who's to Blame for Its Mistakes
It’s important that we use accurate terminology when discussing how AI chatbots make up information

Remembering Lynn Conway, of the Conway Effect, Who Helped Launch the Computing Revolution
Lynn Conway, a trans woman and advocate for LGBTQ rights, was underappreciated and often underrecognized for her work in chip design
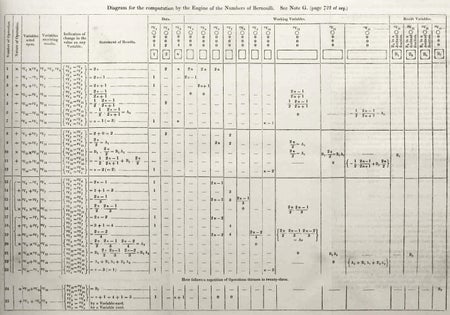
Ada Lovelace’s Endnotes Foretold the Future of Computation
Ada Lovelace’s wisdom about the first general-purpose computer can be found buried in the appendix of another paper

AI Doesn’t Threaten Humanity. Its Owners Do
We shouldn’t be afraid of AI taking over humanity; we should fear the fact that our humanity hasn’t kept up with our technology
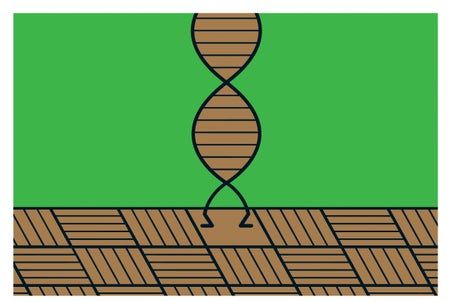
A ‘Computer’ Built from DNA Can Find Patterns in Photographs
Artificial DNA sorts images like a neural network does

What Apple’s New Vision Pro Headset Might Do to Our Brain
The release of Apple’s mixed-reality headset raises questions about hours spent in a virtual replacement of our world

We Need Cybersecurity in Space to Protect Satellites
Amid rising numbers of cyber threats, safeguarding our satellites is no longer optional but a necessity for global security and reliability
Can this AI Tool Predict Your Death? Maybe, But Don’t Panic
Amid the machine-learning boom, model developers have built an all-purpose digital oracle from a trove of big data

The Most Important Unsolved Problem in Computer Science
Here’s a look at the $1-million math problem at the heart of computation