
How a lost 1812 wristwatch sparked a 200-year race in precision engineering
Modern luxury watches can be traced back to one of Napoleon Bonaparte’s younger sisters

How a lost 1812 wristwatch sparked a 200-year race in precision engineering
Modern luxury watches can be traced back to one of Napoleon Bonaparte’s younger sisters

The world’s deepest sensors will detect earthquakes around the world from far below Antarctica
Here’s how scientists drilled 8,000 feet through ice to place the world’s deepest seismometers


The surprisingly baffling science of static electricity
This familiar phenomenon has puzzled researchers for centuries, but experiments are finally making sense of its unruly behaviors

Heathrow dropped its 100-ml liquids rule. This scanner tech made it possible
New CT scanners can build a 3D model of your carry-on, helping airport staff spot risks without making you unpack or decant liquids into tiny bottles
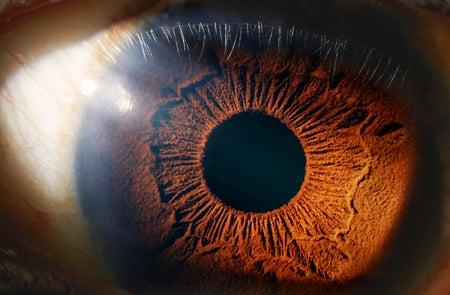
Breakthrough in Digital Screens Takes Color Resolution to Incredibly Small Scale
These miniature displays can be the size of your pupil, with as many pixels as you have photoreceptors—opening the way to improved virtual reality

Go Inside a Room That Lets You Hear Your Nervous System
Step into a room so quiet you can hear your own heartbeat—and your nervous system.
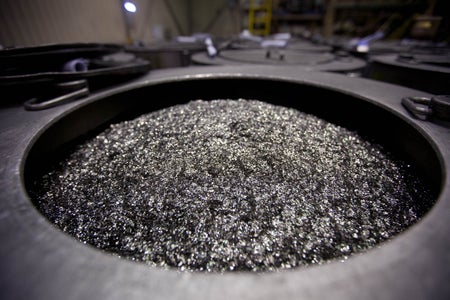
Why Are Rare Earth Metals So Precious?
China is blocking exports of these vital minerals. What makes them so special?

This Sponge Captures the Teeny Bits of Gold in Electronic Waste
A self-building sponge that efficiently collects gold could eliminate some harsh methods used to process e-waste

The Emerging Artificial Intelligence Era Faces a Growing Threat from Directed Energy Weapons
Autonomous and AI-enabled systems increasingly rely on optical and radio frequency sensors and significant computer power. They face growing vulnerabilities from directed-energy laser and microwave weapons

The Sophisticated Threads behind a Hat That Senses Traffic Lights
A new technique to make electronic fibers could help solve wearable technology’s flexibility problem

Scientists Finally Invent Heat-Controlling Circuitry That Keeps Electronics Cool
A new thermal transistor can control heat as precisely as an electrical transistor can control electricity

Technology Is Secretly Stealing Your Time. Here’s How to Get It Back
Technology is supposed to save us time, right? Turns out, it’s stealing some of our most precious time, but it’s not too late to get it back